On February 28, 2026, the United States and Israel launched a joint military offensive — codenamed Operation Epic Fury (USA) and Operation Roaring Lion (Israel) — against strategic targets in Iran, including nuclear facilities, IRGC command centers, and regime leadership compounds. The death of Supreme Leader Ayatollah Ali Khamenei, confirmed by the Iranian government on March 1, marked an unprecedented turning point in the conflict and triggered an immediate escalation in the cyber domain.
From the initial hours of the kinetic operation, offensive cyber operations were conducted in parallel with airstrikes. Israeli sources classified the digital offensive as the largest cyberattack ever recorded, resulting in the near-total collapse of Iran’s connectivity — which dropped to approximately 1–4% of normal levels, according to NetBlocks data — the disruption of government services, state media outlets such as the IRNA agency, and the compromise of civilian applications like the religious app BadeSaba.
Simultaneously, the pro-Iranian cyber ecosystem mobilized in retaliation. Hacktivist collectives and state-aligned personas — including Handala Hack (linked to MOIS), Cyber Islamic Resistance, Dark Storm Team, APT Iran, and the newly formed “Electronic Operations Room” — claimed responsibility for over 150 operations between February 28 and March 1. These actions encompassed DDoS attacks, defacement, wiper malware, and ransomware operations targeting Israeli and Western entities across sectors such as energy, finance, healthcare, and critical infrastructure.
Targeted Attacks
In the hours following the commencement of joint military operations against Iran, Telegram channels linked to pro-Iranian hacktivist collectives and their allies entered a state of intense mobilization. Claims of attacks against Israeli infrastructure and allied nations were published at an accelerated pace. The rhetoric within these spaces fluctuated between operational coordination and propaganda, with operators broadcasting targets, alleged results, and calls for further action. The following captures, obtained directly from these channels during the analyzed period, illustrate the nature and scale of this mobilization.
The Altoufan Team (linked to the IRGC – Islamic Revolutionary Guard Corps) was among the first to manifest in the monitored channels, publishing hostile statements against Israel and claiming the execution of Distributed Denial of Service (DDoS) attacks against targets in Kuwait and Israel. The following images record these publications, including messages of ideological motivation and claims of service unavailability for the targeted entities, alongside a directed attack against the military logistics company “scagroup.”
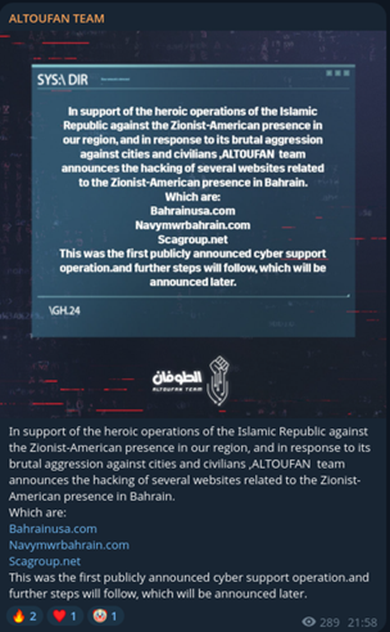

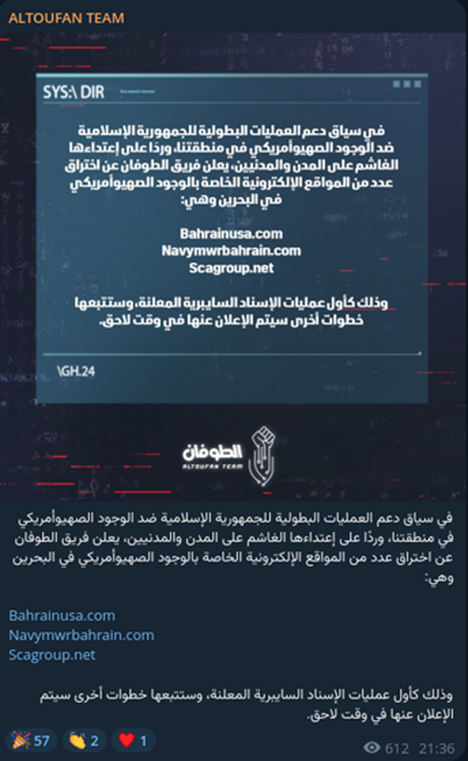
“In continuation of our support for the heroic operations of the Islamic Republic against the Zionist and American presence in our region, and in response to their brutal aggression against cities and civilians, the ‘Al-Toufan’ team announces the breach (hacking) of several websites linked to the Zionist and American presence in Bahrain, which are:
Bahrainusa.com > Navymwrbahrain.com > Scagroup.net > This is part of ongoing cyber support operations, and further steps will follow, to be announced in due course.”
Altoufan Team claims the compromise of three websites linked to the U.S. presence in Bahrain, classifying the action as its first public cyber support operation for Iran.
The selection of targets is strategically consistent with the group’s narrative: Bahrainusa.com is the official portal of the Embassy of the Kingdom of Bahrain in Washington, aimed at promoting bilateral U.S.–Bahrain diplomatic relations; Navymwrbahrain.com is the official site of the U.S. Navy’s Morale, Welfare and Recreation (MWR) program at Naval Support Activity (NSA) Bahrain, the base that houses the U.S. Navy’s 5th Fleet in the Persian Gulf; and Scagroup.net, associated with support operations in the region. The targets reflect the intent to strike symbols of American military and diplomatic presence in the Gulf — a central pillar of the group’s rhetoric. The message concludes with a promise of further operations, signaling that the campaign was in the initial phase of escalation.
Attacks on Control Systems and SCADA
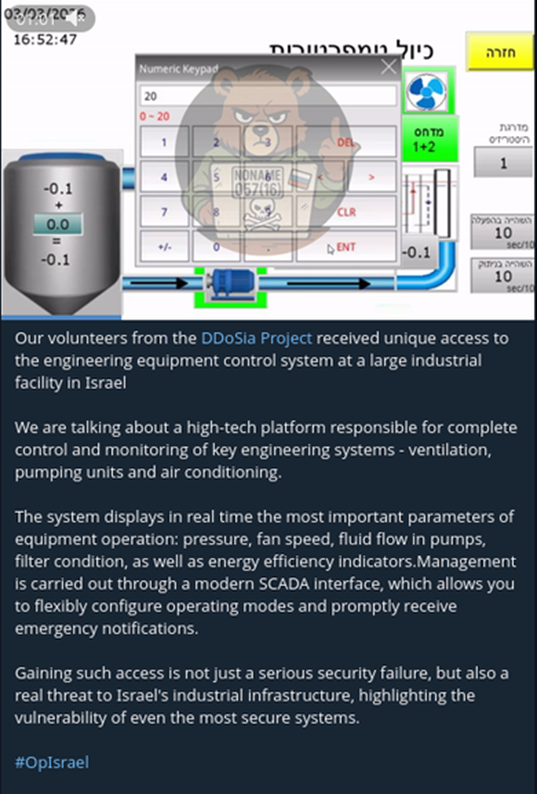
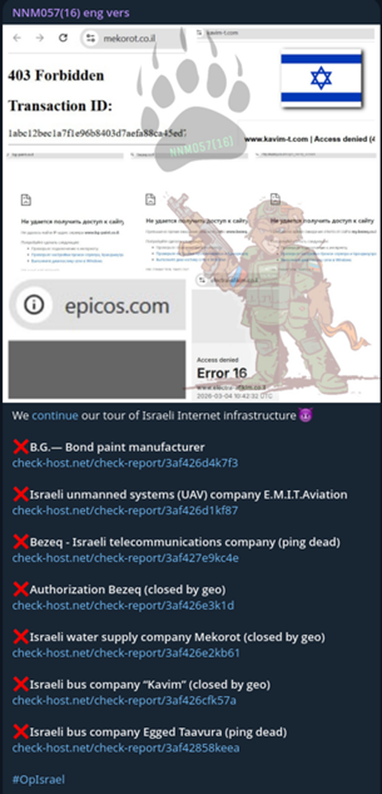
In a significant escalation in sophistication and potential impact, the Altoufan Team began claiming the compromise of SCADA (Supervisory Control and Data Acquisition) systems, shifting from denial-of-service attacks to attempted access to industrial control environments. Concurrently, the Russian group NoName057(16) also released evidence of actions against control systems linked to Israeli infrastructure, reinforcing the pattern of operational convergence between pro-Iranian and pro-Russian actors observed throughout the conflict.

“We have breached Jordan’s vital infrastructure. Over a month ago, following successful identification, we managed to penetrate the internal network of the Jordan Silos and Supply General Company. Through a security vulnerability, we gained internal network access and established persistence. After entering the internal network, we identified and mapped several critical system components, including: the silo control and inventory management system, the weighing and scale systems, solar energy systems, and surveillance camera access.
What did we do? For example, we gradually increased the temperature in the northern silos (Irbid) to spoil the stored wheat. If this process continues, approximately 75,000 tons of wheat — equivalent to three months of consumption for a country of 12 million people — will be wasted. We also breached the electrical grid powering the silos, disabled emergency and cooling systems, and compromised the surveillance cameras to hinder detection.”
In the first image, the Russian group NoName057(16), through volunteers from the DDoSia project, claims access to an engineering control system of an industrial facility in Israel. The screenshot displays a SCADA interface with Hebrew text, a numeric keypad, and real-time monitoring parameters — including pressure, fan speed, pump flow rates, and energy efficiency indicators — consistent with Building Management Systems (BMS) for ventilation, pumping, and HVAC. The group frames this action as a concrete threat to Israeli industrial infrastructure under the hashtag #OpIsrael.
In the second image, the same group details a broader Denial-of-Service (DoS) campaign against Israeli targets across multiple sectors, accompanied by screenshots of downtime and check-host.net reports as proof of impact. Claimed targets include Mekorot, Israel’s national water agency; Bezeq, the country’s largest telecommunications operator; public transport companies Kavim and Egged Taavura; E.M.I.T. Aviation, a manufacturer of Unmanned Aerial Vehicles (UAVs); and Bond, from the industrial sector. The breadth and sectoral diversity of these targets — water, telecommunications, transport, defense, and industry — evidence a deliberate strategy to exert pressure on multiple pillars of Israel’s critical infrastructure.
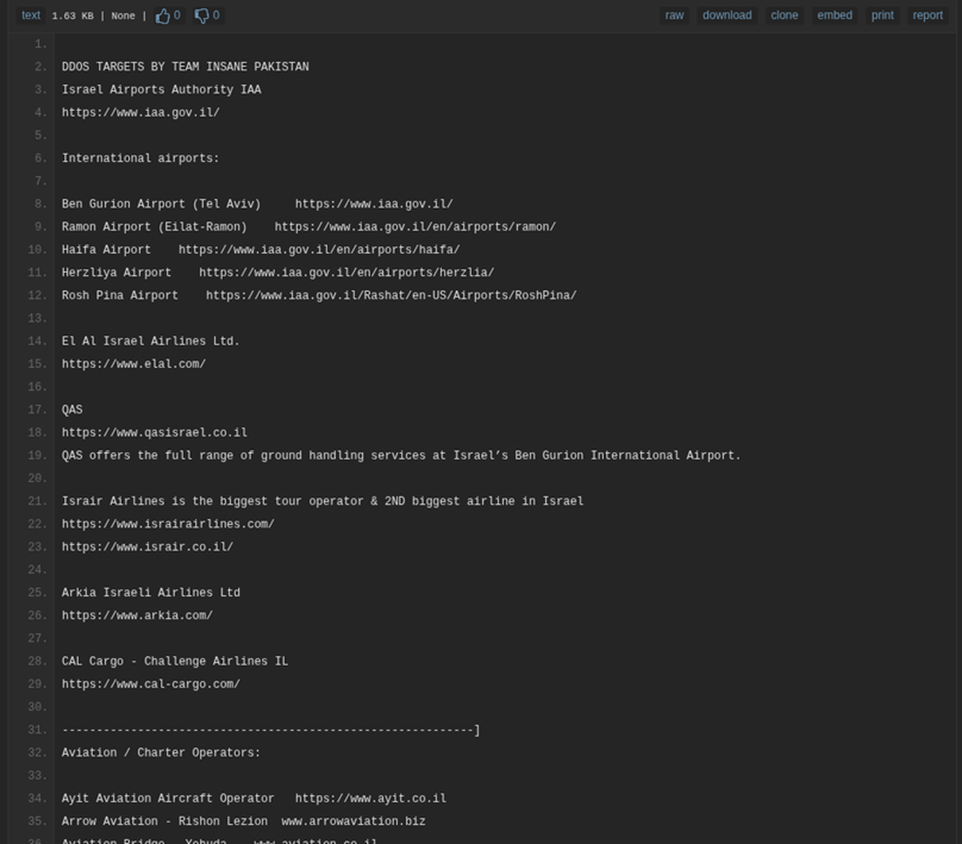
Below is a list of DDoS targets compiled by the group Team Insane Pakistan and distributed via Pastebin, focusing exclusively on the Israeli aviation sector. The document enumerates URLs belonging to the Israel Airports Authority (IAA), international airports such as Ben Gurion, Ramon, Haifa, Herzliya, and Rosh Pina, as well as airlines including El Al, Israir, Arkia, and CAL Cargo. The list further extends to aviation and charter operators, indicating a systematic mapping of the entire Israeli aviation industry chain as an attack surface. The structured organization of targets by category suggests a prior reconnaissance effort designed to guide coordinated denial-of-service campaigns.
Data Sales on Underground Forums
The ZenoX Threat Intelligence Team identified a post on an underground data trading forum by the threat actor “aalikbari,” offering multiple compromised Iranian datasets for sale.
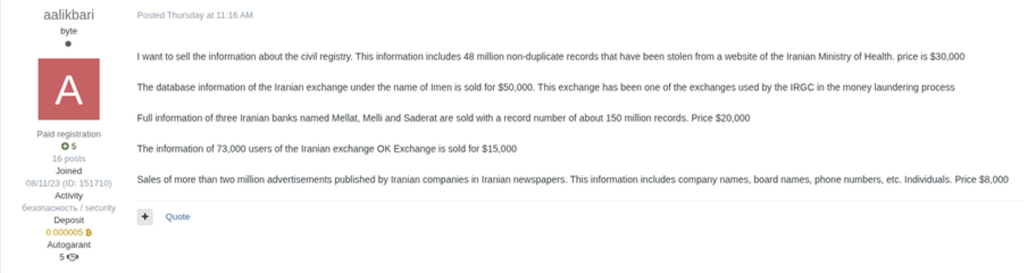
Among the advertised batches are 48 million civil records extracted from the Iranian Ministry of Health ($30,000); databases from the Iranian exchange Imen — which the actor claims is linked to IRGC money laundering operations ($50,000); approximately 150 million comprehensive records from major Iranian banks Mellat, Melli, and Saderat ($20,000); data belonging to 73,000 users of the OK Exchange platform ($15,000); and over two million business records published in Iranian newspapers, including company names, directors, and phone numbers ($8,000).
ZenoX initiated direct contact with the threat actor to verify the authenticity and scope of the offered data as part of the intelligence validation process for this report. Below is an excerpt of the conversation where the threat actor’s contact information was obtained:
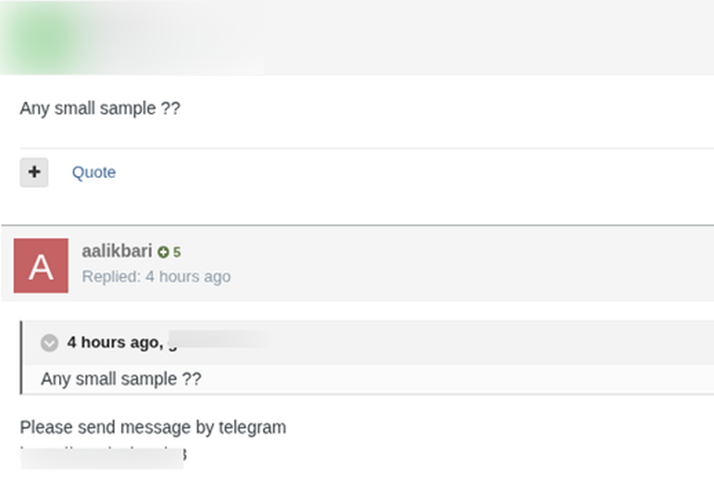
Following the initial contact on the forum, the interaction with the threat actor migrated to Telegram. In the conversation above, the actor shares samples of the advertised data, sending files named consistently with the offered batches. The threat actor claims to be on the verge of leaving Iran and requests urgency in the negotiations, citing severe difficulty connecting to the internet — a report consistent with the near-total blackout imposed on the country since the start of military operations on February 28. This statement reinforces the possibility that the actor is operating from within Iranian territory and that the collapse of telecommunications infrastructure is directly impacting the operational capacity of domestic threat actors. According to the actor via the forum, payment must be made via Monero (XMR).

File Analysis
The ZenoX Threat Intelligence Team conducted an analysis of the six samples received from the threat actor. The verification revealed structured and consistent data across all files, suggesting an origin from legitimate systems. Below is a summary of the analysis by sample:
melli.txt: Contains records from Bank Melli, with fields including National Code (the Iranian equivalent of a Social Security number), bank card numbers, full names, dates of birth, and mobile phone numbers. The card numbers follow the 6037 prefix, consistent with the BIN (Bank Identification Number) standards of Iranian financial institutions.
saderat.txt: Presents records from Bank Saderat, including account numbers, full names, card numbers, phone numbers, and branch identifiers — a structure consistent with direct extraction from the institution’s internal systems.
mellat.txt: The most detailed among the banking samples, containing National Codes, account numbers, full names, father’s names, ID numbers, dates of birth, card numbers, and mobile phone numbers. This dataset is sufficient to facilitate large-scale financial fraud and identity theft.
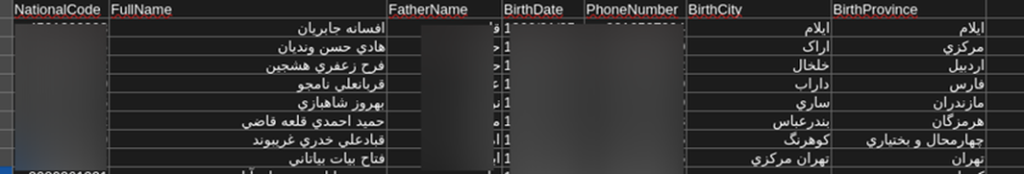
sample.csv: Contains approximately 2,000 records of Iranian citizens with National Codes, names, father’s names, dates of birth, phone numbers, city, and province of birth — consistent with the civil registry data mentioned in the original advertisement.
rrk.csv: Features 69 records of official Iranian business announcements published in newspapers, containing corporate names, director data, ID numbers, and corporate registration details — compatible with the commercial dataset offered by the actor.
files.txt: Consists of a directory listing of over 30,000 files and databases in the threat actor’s possession, indicating a massive archive of compromised data that significantly exceeds the Iranian scope.
The consistency of formats, the presence of sensitive fields in recognizable patterns of the Iranian financial and civil systems, and the internal coherence of the data indicate, in ZenoX’s preliminary assessment, a high probability that the samples are legitimate.
MuddyWater – Detected Infections
In an analysis conducted by ZenoX, a sample related to the Iranian APT MuddyWater was evaluated, revealing the following execution chain: The initial binary creates a process in a suspended state (T1055 — Process Injection) by invoking pythonw.exe from a temporary directory, subsequently injecting data into this remote process to execute a Python script (main.py) via a dropped interpreter (T1059.006 — Python Execution). This approach of packaging a legitimate Python interpreter with the payload is consistent with documented MuddyWater tradecraft in recent campaigns.
Dropped Files: The sample extracts a complete Python ecosystem into the %TEMP% directory, including python.exe, pythonw.exe, python312.dll, libcrypto-3.dll, libssl-3.dll, sqlite3.dll, vcruntime140.dll, among other DLLs and .pyd modules. The dropped python.exe file was classified as Downloader.Sheloader by at least one antivirus engine (1/26), while libcrypto-3.dll triggered matches in YARA rules (T1105 — Ingress Tool Transfer).
C2 Communication: The sample establishes communication with the domain mazafakaerindahouse[.]info, registered only 6 days prior to the analysis (T1583.001 — Acquire Infrastructure: Domains), resolving to IP 149.33.7.161 (United States). The connection is established via port 443/TCP by the pythonw.exe process, sending traffic over a standard HTTP port but without conventional HTTP headers — an indicator of a custom protocol or tunneling over HTTPS.
Evasive Techniques and Additional Capabilities: The malware demonstrates anti-analysis and evasion capabilities, including queries for kernel debugger information, host geolocation attempts, the presence of obfuscated shellcode (T1140), marking files for deletion (log/trace cleaning), runtime compression/decompression, Base64 encoding, access token manipulation, registry modification, and code injection via the CreateThread API. This set of capabilities is consistent with a loader/downloader designed to establish persistent initial access and download second-stage payloads, Group-IB also provided a threat research on MuddyWater APT
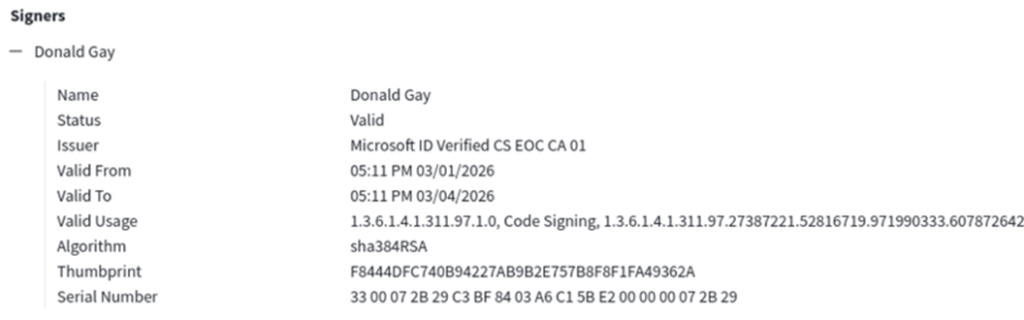
A detail that warrants highlighting is the digital signature present in the cluster’s artifacts. Binaries associated with the campaign utilize a code signing certificate issued in the name of “Donald Gay,” valid for only 3 days — from March 1, 2026, to March 4, 2026 — coinciding exactly with the immediate period following the assassination of Khamenei and the onset of Iranian retaliation. The certificate, issued by the authority Microsoft ID Verified CS EOC CA 01 using the sha384RSA algorithm with a valid status, was obtained through the Microsoft Identity Verification program for code signing — a legitimate mechanism abused by the operators to grant an appearance of legitimacy to the payloads.
The choice of the name “Donald Gay” is a deliberate provocation aimed at U.S. President Donald Trump,
Traffic Analysis
The request is a GET to the path /a2ea4d41-3c8b-5b78-ab46-e14bf6af7383/lock1 on the host mazafakaerindahouse[.]info. The URI structure is noteworthy: it utilizes a UUID as an identifier — likely generated per host or session — followed by the /lock1 endpoint, which is suggestive of a check-in or polling mechanism for receiving tasks. The User-Agent Python-urllib/3.12 confirms that the communication originates from the Python 3.12 interpreter dropped by the malware, with no User-Agent spoofing effort — a useful indicator for detection rules.
The C2 server operates on nginx/1.18.0 (Ubuntu) and responds with an HTTP 404 in JSON format (Content-Type: application/json), with the body {“code”:404,”success”:false,”message”:”File not found”}. Despite the 404 code, the structured JSON response with standardized fields (code, success, message) and the Access-Control-Allow-Origin:* header indicate that the server is a custom web application — not a simple web server returning a default error page. The 404 likely indicates the absence of pending tasking for the implant at that specific time, characterizing a classic polling-based C2 pattern.

Infrastructure Analysis
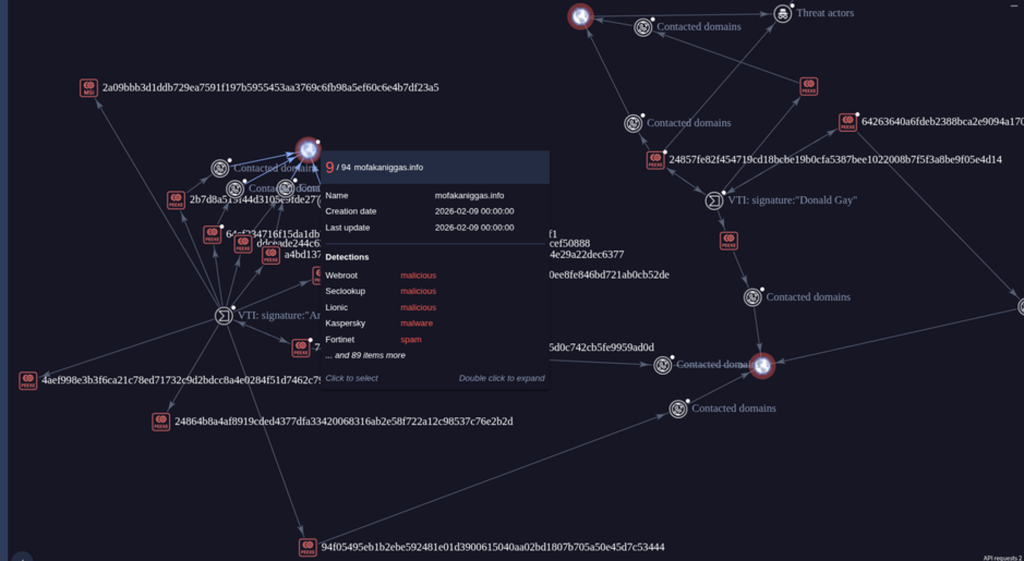
The Relationship Cluster Analysis reveals an interconnected infrastructure of malicious artifacts that significantly broadens the scope of the identified campaign. The central node visible in the graph is the domain mofakaniggas[.]info, registered on February 9, 2026 — approximately three weeks before the start of kinetic operations — and classified as malicious by multiple detection engines, including Webroot, Seclookup, Lionic, Kaspersky, and Fortinet (9 detections out of 94 checks).
This domain constitutes a second C2 infrastructure linked to the same campaign, operating in parallel with the previously documented mazafakaerindahouse[.]info. Both follow a pattern of provocative naming and recent registration, which characterizes the pre-staging of disposable infrastructure by MuddyWater.
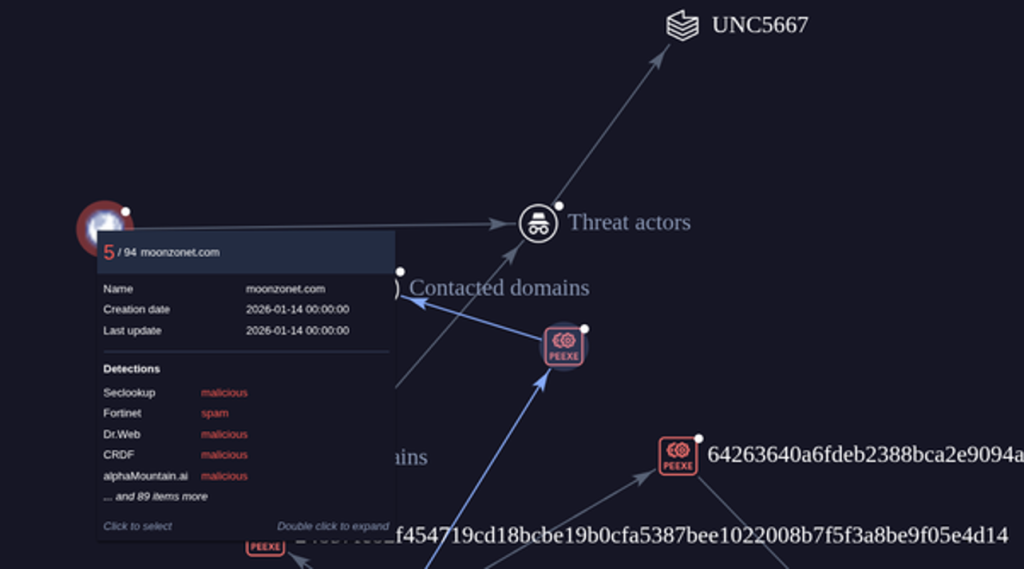
The graph exposes a network of at least ten PE executables (peexe) connected to this domain through “Contacted domains” relationships, including an MSI file (hash starting with 2a09bbb3d1ddb…), which suggests the use of installers as a delivery vector — a technique documented in the group’s previous campaigns. Multiple additional hashes radiate from the central node, each with its own connections to contacted domains, forming a star topology typical of operations with shared C2 infrastructure across payload variants.
On the right side of the graph, a second cluster of artifacts is observed, linked by additional “Contacted domains” relationships and VTI signatures, including the “Donald Gay” rule, which serves as a clustering pivot for behaviorally similar samples. The multiple layers of contacted domains visible on the far right of the graph suggest that the campaign operates with rotating C2 infrastructure, where different samples communicate with different domains — an operational resilience practice that hinders the complete blocking of the campaign through a single indicator.
The breadth of the cluster — multiple binaries, two or more C2 domains, use of varied delivery formats (PE, MSI), and infrastructure registration weeks in advance — reinforces the assessment that this is a planned and coordinated operation by MuddyWater, featuring pre-conflict preparation and an escalation of activity synchronized with the military offensive.
Indicators of Compromise (IOCs)
Domínios C2
mazafakaerindahouse[.]info
mofakaniggas[.]info
lecturegenieltd[.]pro
meetingapp[.]site
afterworld[.]store
girlsbags[.]shop
onlinepettools[.]shop
web14[.]info
web27[.]info
Endereços IP:
149.33.7.161 (C2 — mazafakaerindahouse[.]info — Estados Unidos)
URLs maliciosas:
hxxps://meetingapp[.]site/webexdownload (ClickFix — download de payload)
hxxps://mofakaniggas.info
hxxp://moonzonet.com
hxxps://mazafakaerindahouse.info
SHA-256Descrição:
a8c380b57cb7c381ca6ba845bd7af7333f52ee4dc4e935e98b48bb81facad72b
ed4f68278290205a9d6807644bdef858d80a16c8ebea90d9e2de59a818b7e9ef
36c1a3b66539e072e43579bfcdef4375c49bf55bb1b3d264939757a9a77fa288
Geopolitics and Threat Intelligence
The events documented in this report reinforce an increasingly consolidated pattern: geopolitical flashpoints act as immediate triggers for the intensification of cyber operations on a global scale. The assassination of Khamenei not only sparked kinetic retaliation but simultaneously activated state-sponsored APTs, hacktivist collectives, and opportunistic actors — resulting in over 150 claimed attacks against 110 organizations across 16 countries in just 72 hours.
Three central phenomena emerge from this analysis:
Ecosystem Convergence: Tactical cooperation between pro-Iranian and pro-Russian actors, such as NoName057(16), expands the threat surface beyond formal alliances.
Attack Cycle Acceleration: C2 domains registered days in advance, certificates with 72-hour validity, and the use of Generative AI in malware development demonstrate a drastic reduction in preparation time.
Dissolution of Boundaries between Military and Civilian Targets: Healthcare, transportation, water, and commercial aviation were indiscriminately targeted as instruments of pressure.
For organizations in sectors historically targeted by Iranian APTs — government, energy, telecommunications, finance, and defense — kinetic conflicts must be treated as leading indicators of cyber campaigns.
Contextualized threat intelligence and the ability to respond rapidly to emerging TTPs remain essential pillars of a robust defensive posture.





